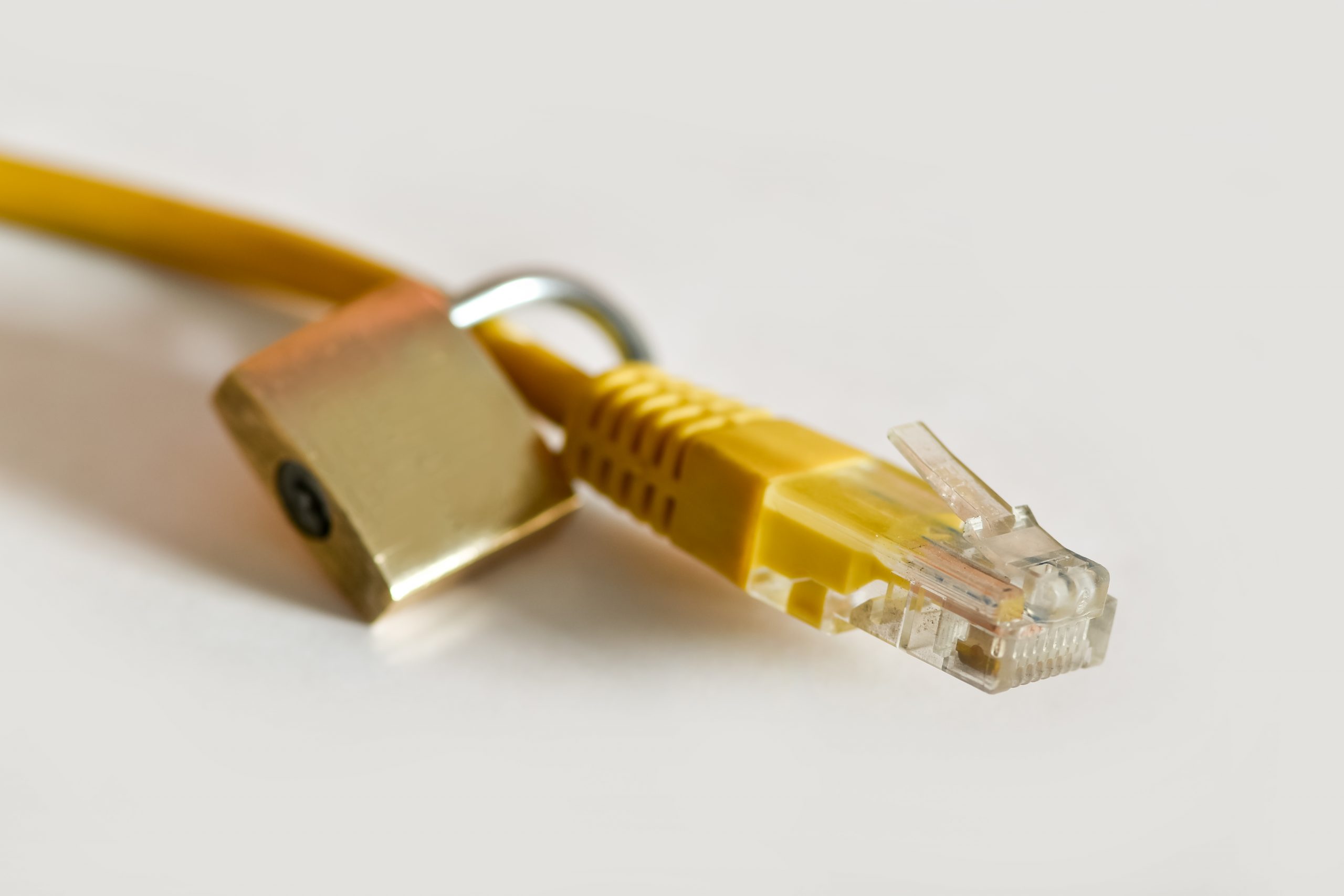
Ever wondered how many suppliers your organisation is connected to? Most likely you’re connected to multiple service providers; whether it is to receive a consultation, auditing, or support services. These are known to your business as a third party. This can also be extended to an elastic workforce or sub-contracted employees such as developers. Some of these third parties will at some point require access to your systems or business data to conduct their services. The issue is giving third parties access to your sensitive data while also keeping your data secure.
So how do you protect and secure your sensitive business data?
Before we answer that question, let's look at what most organisations are currently doing to secure their data and to what extremes they go to. In doing so we shall create some fictitious companies to enable the required scenario. White Lotus Ltd is acquiring services from Black Fox Ltd (provider) to provide a system audit as part of an assessment to evaluate the required changes for White Lotus’s legacy ERP system.
The first thing both businesses do is sign a non-disclosure agreement (NDA). Once that is out of the way Black Fox is ready to start a discovery session on the ERP system. White Lotus has different options and methods to allow the Black Fox personnel access to the system such as:
- Provide Black Fox a VPN tunnel and credentials to the ERP system
- Block Fox to visit and conduct session from premises
- Provide Black Fox with a company device to access the system
- Method A will come at no cost to White Lotus and requires minimal effort. On the other hand, it also causes high security risks of data leakage. The provider will use his/her own device which enables the provider to have full control of White Lotus data without any preventions.
- White Lotus will need to make travel arrangements for the provider to visit the premises. This option is not always possible as certain contracted services may take long, thus conducting them remotely is the best option. In any case this scenario makes sense when providing a business device and dedicating a resource to supervise the Black Fox representative. This scenario is only then considered low risk and high effort, costing the business money and resources to lower the risk.
- Shipping a business device to the provider can be expensive and can also cause delays due to logistical issues. While having a monitored and controlled business device would lower the risk, the administration and logistics make this scenario a nightmare for White Lotus.
So how do you protect your sensitive, core business data?
With Windows 365 enterprise a business can address these data security risks with a few simple clicks and in a cost-effective manner. The IT admin does not need to worry about device procurement, servicing the hardware, insurance or other logistical nightmares. Simply assign the provider a controlled virtual desktop which is managed and monitored through Microsoft Endpoint Manager. With the ability to set policies such as removing the ability to copy or transfer data between the cloud PC and local devices you can rest assured that your data is secure. Not excluding other services such as VPN and firewall configurations to enhance and protect your business data. So why not give the third-party representative access to a cloud PC?
How can BMIT Technologies help?
Every client we work with requires different solutions. So, we tackle each need with our expertise in technology, business strategy and innovation.
We propose and develop intelligent, secure infrastructure solutions, help build your internal capabilities and identify opportunities to enhance your business potential through the application of innovative technologies. This ensures a greater level of business management and progression.
Want to learn more about how your business can secure its data? Contact us and one of our experts will reach out and guide you accordingly